Amazon WorkSpaces Security
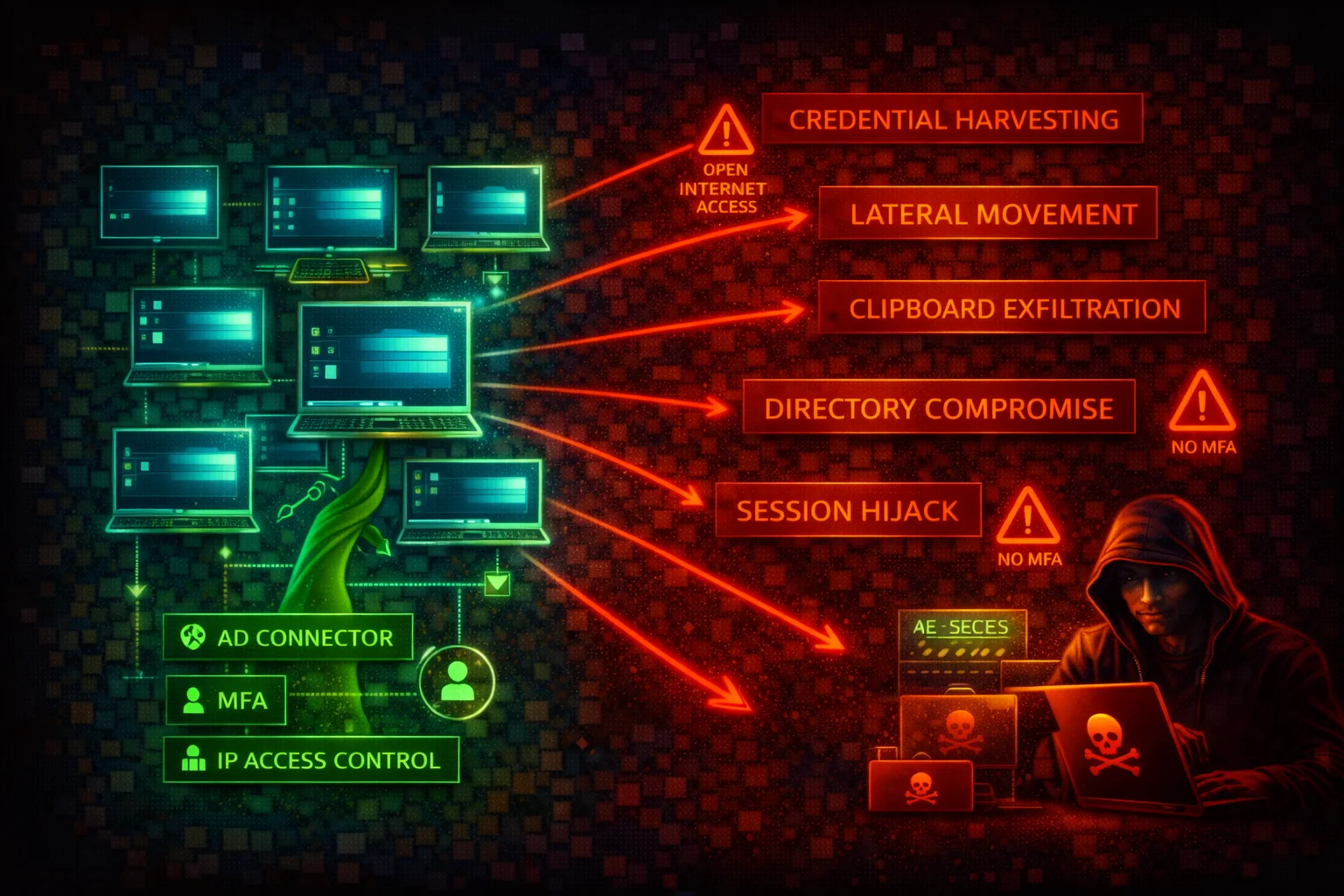
COMPUTEAmazon WorkSpaces is a managed Desktop-as-a-Service (DaaS) that provisions cloud-based Windows or Linux virtual desktops. Each WorkSpace is associated with a directory (AD) and runs inside a customer VPC. A compromised WorkSpace gives an attacker a foothold inside the VPC with AD-joined credentials.
📋Service Overview
Virtual Desktop Environment
WorkSpaces provisions cloud-based Windows or Linux desktops associated with a directory (AWS Managed Microsoft AD, AD Connector, or Simple AD). Supports PCoIP and DCV streaming protocols. Clients connect via native apps or web browser. Features include clipboard, drive, and USB redirection.
Attack note: WorkSpaces are full virtual desktops with persistent storage. They sit outside traditional EC2-based detection, creating monitoring blind spots.
Active Directory Integration
The directory backing WorkSpaces is the single authentication plane. Compromising it grants access to all WorkSpaces in the directory, and potentially to on-premises AD via trust relationships. RADIUS-based MFA is supported but not configured by default.
Attack note: Without IP access control groups and MFA, WorkSpaces can be accessed from any IP with valid AD credentials.
Security Risk Assessment
WorkSpaces provide full desktop environments inside the VPC with Active Directory credentials. Clipboard and drive redirection create data exfiltration channels. Without IP access control groups and MFA, WorkSpaces can be accessed from any IP with valid AD credentials. WorkSpaces run on AWS-managed compute not visible in the EC2 console, creating monitoring blind spots.
⚔️Attack Vectors
Initial Access & Credential Abuse
- •Credential stuffing against AD -- compromised AD credentials grant full desktop access
- •No MFA enforcement -- stolen AD credentials alone provide WorkSpace access from any location
- •No IP access control -- WorkSpaces accept connections from any public IP
- •Phishing for WorkSpace registration codes combined with AD credentials
- •WorkSpaces Web (browser access) abuse from unmanaged devices
Post-Compromise & Lateral Movement
- •VPC network pivoting -- compromised WorkSpace can scan and reach internal resources
- •Clipboard exfiltration -- two-way clipboard redirection enabled by default
- •Drive redirection data theft -- local drive mapping for file transfers
- •AD credential harvesting with Mimikatz on compromised Windows WorkSpace
- •Persistence via D: drive payloads that survive WorkSpace rebuilds
⚠️Misconfigurations
Access Control Gaps
- •No IP access control groups configured -- accepts connections from any IP
- •MFA not enabled -- RADIUS MFA not configured by default
- •Web Access enabled without need -- bypasses client-side controls
- •Overly permissive security groups -- allows outbound to internet for C2
- •Unrestricted device types -- all client types allowed by default
Configuration & Data Protection Gaps
- •Clipboard redirection left enabled -- data exfiltration vector
- •Drive redirection not disabled -- file transfer between WorkSpace and local
- •Root volume not encrypted -- encryption not enabled by default
- •Running mode set to ALWAYS_ON without justification -- increases attack window
- •No user volume backup strategy beyond WorkSpace snapshots
🔍Enumeration
aws workspaces describe-workspacesaws workspaces describe-workspace-directoriesaws workspaces describe-workspaces-connection-statusaws workspaces describe-workspace-bundles --owner AMAZONaws workspaces describe-ip-groupsaws workspaces describe-workspace-directories --query "Directories[*].{DirectoryId:DirectoryId,DeviceTypeWindows:WorkspaceAccessProperties.DeviceTypeWindows,DeviceTypeMacOs:WorkspaceAccessProperties.DeviceTypeMacOs,DeviceTypeWeb:WorkspaceAccessProperties.DeviceTypeWeb}"aws workspaces describe-workspaces-poolsaws workspaces describe-connection-aliases📈Privilege Escalation
IAM-Level Escalation
- •CreateWorkspaces with AD admin credentials to get a domain-joined desktop in the VPC
- •ModifyWorkspaceProperties to upgrade instance for resource-intensive attacks
- •ModifyWorkspaceCreationProperties to weaken security posture for future WorkSpaces
- •ModifyWorkspaceAccessProperties to re-enable restricted device types like Web Access
- •RebuildWorkspaces abuse -- rebuild preserves user volume; persistence survives
AD-Level Escalation from WorkSpace
- •Compromised Windows WorkSpace with local admin can run AD enumeration tools
- •BloodHound, Rubeus, Mimikatz for domain escalation
- •Escalate from single desktop to domain admin
- •Harvest cached AD credentials, Kerberos tickets, NTLM hashes
- •Pivot to on-premises AD via trust relationships
Key insight: WorkSpaces are domain-joined desktops. A compromised WorkSpace is a foothold in both the VPC and the AD domain, enabling lateral movement to any resource reachable from that network position.
🔗Persistence
Persistence Mechanisms
- •Place payloads on D: drive (user volume) -- survives WorkSpace rebuilds
- •Automatic snapshots taken every 12 hours capture payloads for rebuild persistence
- •Create additional WorkSpaces in the directory as backup access points
- •Scheduled tasks or startup scripts on Windows WorkSpaces
- •Install backdoors that survive root volume rebuild
Data Exfiltration Paths
- •Two-way clipboard redirection to copy data to local machine
- •Drive redirection to transfer files to attacker local filesystem
- •USB redirection to mount external storage
- •Network-based exfiltration via outbound internet access
- •Print to local printer to exfiltrate documents
🛡️Detection
CloudTrail Events
- •CreateWorkspaces -- new WorkSpace created
- •TerminateWorkspaces -- WorkSpace destroyed
- •ModifyWorkspaceProperties -- configuration changed
- •ModifyWorkspaceAccessProperties -- access controls modified
- •RebuildWorkspaces -- WorkSpace rebuilt
Indicators of Compromise
- •Connections from unexpected regions or IPs (CloudWatch metrics)
- •CreateWorkspaces calls from unusual principals
- •ModifyWorkspaceAccessProperties enabling Web Access
- •Unusual outbound traffic from WorkSpaces subnets (VPC Flow Logs)
- •Multiple failed authentication attempts against the directory
📜WorkSpaces Policy Examples
{
"Version": "2012-10-17",
"Statement": [{
"Effect": "Allow",
"Action": "workspaces:*",
"Resource": "*"
}]
}Grants full WorkSpaces control including creating, terminating, modifying, and rebuilding any WorkSpace. An attacker can create rogue WorkSpaces, disable security controls, or terminate legitimate ones.
{
"Version": "2012-10-17",
"Statement": [{
"Effect": "Allow",
"Action": [
"workspaces:DescribeWorkspaces",
"workspaces:DescribeWorkspaceDirectories",
"workspaces:DescribeWorkspaceBundles",
"workspaces:DescribeWorkspacesConnectionStatus",
"workspaces:DescribeIpGroups",
"workspaces:DescribeWorkspacesPoolSessions"
],
"Resource": "*"
}]
}Read-only access for monitoring and auditing. Cannot create, modify, or terminate WorkSpaces.
{
"Version": "2012-10-17",
"Statement": [{
"Effect": "Allow",
"Action": [
"workspaces:CreateWorkspaces",
"workspaces:TerminateWorkspaces",
"workspaces:RebuildWorkspaces",
"workspaces:StartWorkspaces",
"workspaces:StopWorkspaces"
],
"Resource": "*",
"Condition": {
"StringEquals": {
"aws:ResourceTag/DirectoryId": "d-1234567890"
}
}
}]
}Restricts WorkSpace lifecycle actions to resources tagged with a specific directory ID, preventing cross-directory abuse.
🛡️Defense Recommendations
Enforce IP Access Control Groups
Create IP access control groups to restrict WorkSpace access to known corporate IP ranges or VPN egress IPs. Associate the group with each directory.
aws workspaces create-ip-group \
--group-name "CorporateVPN" \
--group-desc "Allow access from corporate VPN only" \
--user-rules "ipRule=203.0.113.0/24,ruleDesc=Corporate VPN"
aws workspaces associate-ip-groups \
--directory-id d-1234567890 \
--group-ids wsipg-abcdef123Enable RADIUS MFA
Configure RADIUS-based multi-factor authentication on the directory. Use multiple RADIUS server IPs for redundancy.
Disable Clipboard and Drive Redirection
For Windows WorkSpaces, use Group Policy to disable or restrict clipboard redirection direction. For Linux, modify the DCV configuration file. Closes a primary data exfiltration channel.
Restrict Device Types
Disable unnecessary device types (especially Web Access) to reduce the attack surface from unmanaged devices.
aws workspaces modify-workspace-access-properties \
--resource-id d-1234567890 \
--workspace-access-properties \
DeviceTypeWindows=ALLOW,DeviceTypeOsx=ALLOW,DeviceTypeWeb=DENY,DeviceTypeIos=DENY,DeviceTypeAndroid=DENY,DeviceTypeLinux=DENYEnable Encryption at Rest
Encrypt both root and user volumes with AWS KMS when creating WorkSpaces. Encryption must be set at creation time and cannot be enabled later.
Use AUTO_STOP Running Mode
Set WorkSpaces to AUTO_STOP to reduce the attack window during idle periods and reduce cost.
aws workspaces modify-workspace-properties \
--workspace-id ws-abc123def \
--workspace-properties RunningMode=AUTO_STOP,RunningModeAutoStopTimeoutInMinutes=60Monitor with CloudTrail and VPC Flow Logs
Enable CloudTrail logging for all workspaces:* API calls. Enable VPC Flow Logs on WorkSpaces subnets to detect lateral movement. Monitor CloudWatch metrics for unusual connection patterns.
Restrict Outbound Network Access
Apply restrictive security groups and NACLs to WorkSpaces subnets. Block direct internet access; route traffic through a proxy or NAT Gateway with URL filtering.
Amazon WorkSpaces Security Card • Toc Consulting
Always obtain proper authorization before testing