Amazon Detective Security
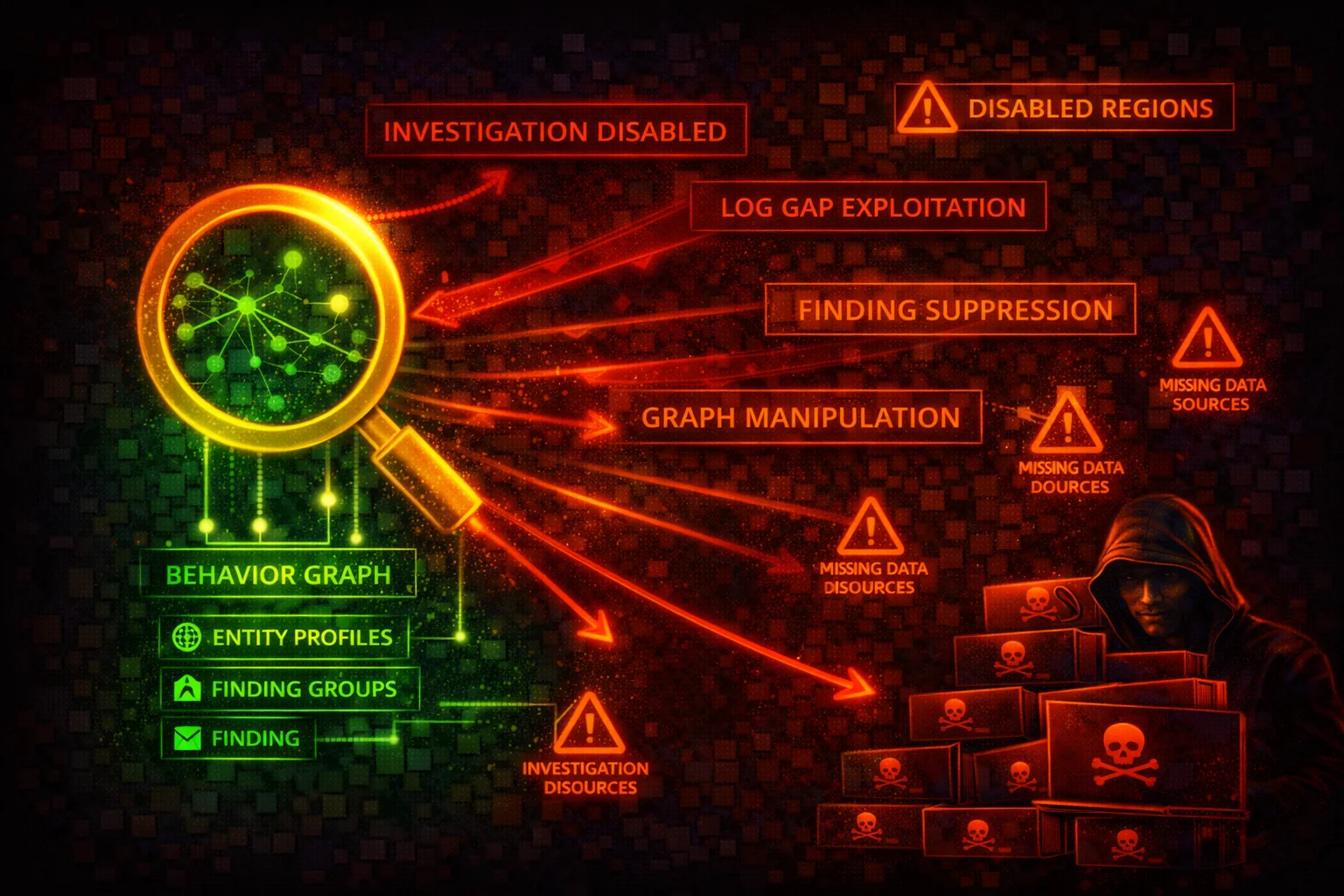
SECURITY INVESTIGATIONAmazon Detective automatically collects log data from AWS resources and uses machine learning, statistical analysis, and graph theory to build interactive visualizations for security investigations. Attackers target Detective to destroy forensic evidence.
📋Service Overview
Behavior Graph & Data Sources
Detective builds a behavior graph from ingested data using ML and statistical analysis, linking entities (IP addresses, IAM principals, AWS accounts) with their activities. Core sources: CloudTrail, VPC Flow Logs, GuardDuty findings. Optional: EKS Audit Logs, Security Hub findings.
Attack note: Deleting the behavior graph permanently destroys up to 1 year of correlated forensic data that cannot be recovered.
Multi-Account Architecture
An administrator account creates and manages the behavior graph, invites member accounts, and conducts investigations. Member accounts contribute data. In AWS Organizations, a delegated administrator can auto-enable Detective for all accounts.
Attack note: Detective is an investigation tool, not a detection tool. Disabling it does not stop alerts but destroys the forensic graph data needed to investigate incidents.
Security Risk Assessment
Detective is an investigation tool, not a detection tool. Disabling it does not stop alerts (GuardDuty still fires), but it destroys the forensic graph data needed to investigate incidents. Attackers who delete the behavior graph eliminate up to 1 year of correlated investigation data.
⚔️Attack Vectors
Destroy Investigation Capability
- •Delete the behavior graph to destroy all forensic data
- •Remove member accounts to stop data ingestion
- •Disable Organizations delegated administrator
- •Disassociate membership to remove account from monitoring
- •Reject invitations to prevent accounts joining the graph
Tamper with Investigations
- •Update investigation state to mark active as closed
- •Delete members to stop data flow during investigation
- •Update organization configuration to stop auto-enabling
- •Tag resources with misleading metadata
- •Remove specific accounts rather than the entire graph
⚠️Misconfigurations
Evasion Techniques
- •Remove specific member accounts (less obvious than full delete)
- •Disable optional data source packages (EKS, Security Hub)
- •Operate within accounts not added to the behavior graph
- •Time deletion to coincide with maintenance windows
- •Use accounts not enrolled as attack staging areas
Operational Evasion
- •Operate from IPs that blend with normal traffic patterns
- •Avoid triggering GuardDuty findings that generate entities
- •Focus on services whose logs are not ingested
- •Exploit interval between finding generation and graph update
- •Target NAT gateway, Fargate, RDS (excluded from VPC Flow Logs)
🔍Enumeration
aws detective list-graphsaws detective list-members \
--graph-arn arn:aws:detective:us-east-1:111122223333:graph:a1b2c3d4e5f6a1b2c3d4e5f6a1b2c3d4aws detective list-datasource-packages \
--graph-arn arn:aws:detective:us-east-1:111122223333:graph:a1b2c3d4e5f6a1b2c3d4e5f6a1b2c3d4aws detective list-organization-admin-accountsaws detective list-investigations \
--graph-arn arn:aws:detective:us-east-1:111122223333:graph:a1b2c3d4e5f6a1b2c3d4e5f6a1b2c3d4📈Privilege Escalation
Investigation Data Exposure
- •detective:SearchGraph reveals IAM roles, IPs, and API patterns
- •Cross-account visibility from administrator account
- •Map entire organization security posture from one account
- •Discover lateral movement targets from graph data
- •Identify high-privilege roles and their activity patterns
Investigation Manipulation
- •UpdateInvestigationState to close active investigations
- •Remove member accounts to stop data flow mid-investigation
- •Disable org admin to break centralized management
- •Disassociate membership to escape monitoring
- •Modify data source packages to create blind spots
Key insight: SearchGraph provides cross-account reconnaissance across all member accounts, making the administrator account a high-value target.
🔗Persistence
High-Severity CloudTrail Events
- •DeleteGraph - behavior graph deleted, all data destroyed
- •DeleteMembers - member accounts removed from graph
- •DisableOrganizationAdminAccount - delegated admin removed
- •DisassociateMembership - account left the graph
Medium-Severity CloudTrail Events
- •UpdateDatasourcePackages - data source config changed
- •UpdateInvestigationState - investigation state modified
- •UpdateOrganizationConfiguration - org auto-enable changed
- •RejectInvitation - account declined graph invitation
🛡️Detection
Key Events to Monitor
- •DeleteGraph - immediate alert, all forensic data lost
- •DeleteMembers - member accounts removed
- •DisableOrganizationAdminAccount - centralized management broken
- •UpdateInvestigationState - investigation tampered with
- •DisassociateMembership - account escaped monitoring
Data Source Coverage
- •CloudTrail logs (automatic)
- •VPC Flow Logs - IPv4/IPv6, EC2 in VPCs only
- •GuardDuty findings (automatic)
- •EKS Audit Logs (optional package)
- •Security Hub findings (optional package)
💻Exploitation Commands
aws detective delete-graph \
--graph-arn arn:aws:detective:us-east-1:111122223333:graph:a1b2c3d4e5f6a1b2c3d4e5f6a1b2c3d4aws detective delete-members \
--graph-arn arn:aws:detective:us-east-1:111122223333:graph:a1b2c3d4e5f6a1b2c3d4e5f6a1b2c3d4 \
--account-ids 444455556666 777788889999aws detective disassociate-membership \
--graph-arn arn:aws:detective:us-east-1:111122223333:graph:a1b2c3d4e5f6a1b2c3d4e5f6a1b2c3d4aws detective disable-organization-admin-accountaws detective update-investigation-state \
--graph-arn arn:aws:detective:us-east-1:111122223333:graph:a1b2c3d4e5f6a1b2c3d4e5f6a1b2c3d4 \
--investigation-id 123456789012345678901 \
--state ARCHIVEDaws detective get-investigation \
--graph-arn arn:aws:detective:us-east-1:111122223333:graph:a1b2c3d4e5f6a1b2c3d4e5f6a1b2c3d4 \
--investigation-id 123456789012345678901📜Detective Policy Examples
{
"Effect": "Allow",
"Action": "detective:*",
"Resource": "*"
}Full access allows deleting behavior graphs, removing members, and destroying all forensic investigation data.
{
"Effect": "Allow",
"Action": [
"detective:Get*",
"detective:List*",
"detective:BatchGet*",
"detective:SearchGraph",
"detective:DescribeOrganizationConfiguration"
],
"Resource": "*"
}Read-only access for security analysts to investigate findings without modification rights.
{
"Sid": "PreventDetectiveTampering",
"Effect": "Deny",
"Action": [
"detective:DeleteGraph",
"detective:DeleteMembers",
"detective:DisableOrganizationAdminAccount",
"detective:DisassociateMembership",
"detective:UpdateInvestigationState"
],
"Resource": "*"
}Organization SCP to prevent deleting behavior graphs or removing member accounts.
{
"Effect": "Allow",
"Action": [
"detective:DeleteGraph",
"detective:DeleteMembers",
"detective:DisassociateMembership"
],
"Resource": "*"
}These permissions allow destroying the behavior graph and all correlated investigation data.
🛡️Defense Recommendations
Use Organization Delegated Administrator
Centralize Detective management so member accounts cannot disable it or leave the behavior graph.
aws detective enable-organization-admin-account \
--account-id 123456789012SCP to Prevent Graph Deletion
Use Service Control Policies to deny Detective destructive actions across all member accounts.
"Action": ["detective:DeleteGraph", "detective:DeleteMembers", "detective:DisableOrganizationAdminAccount"]Enable in All Regions
Detective must be enabled per-region. Ensure behavior graphs exist in every active region.
for region in $(aws ec2 describe-regions --query 'Regions[].RegionName' --output text); do
aws detective create-graph --region $region --tags Environment=Production
doneAlert on Detective Changes
Create EventBridge rules to alert on destructive Detective API calls via CloudTrail.
aws events put-rule --name "DetectiveTamperingAlert" \
--event-pattern '{"source":["aws.detective"],"detail-type":["AWS API Call via CloudTrail"],"detail":{"eventName":["DeleteGraph","DeleteMembers"]}}'Auto-Enable for New Organization Accounts
Ensure new accounts are automatically added to the behavior graph.
aws detective update-organization-configuration \
--graph-arn GRAPH_ARN \
--auto-enableEnable All Data Source Packages
Enable optional data source packages (EKS Audit, Security Hub findings) for maximum investigation coverage.
aws detective update-datasource-packages \
--graph-arn GRAPH_ARN \
--datasource-packages EKS_AUDIT ASFF_SECURITYHUB_FINDINGRestrict SearchGraph Access
SearchGraph provides cross-account visibility into all member account activity. Restrict it to authorized security investigators only.
Monitor CloudTrail for Tampering
Set up alarms for DeleteGraph, DeleteMembers, DisableOrganizationAdminAccount, and UpdateInvestigationState events.
Amazon Detective Security Card • Toc Consulting
Always obtain proper authorization before testing